Across the UK public sector, communications infrastructure is undergoing significant change. As national networks are upgraded and legacy telephony systems approach end-of-life, public bodies face...
Welcome to our Blog
The Connectivity Problem Hiding in Smart Bins and Heart Monitors
A drone surveying farmland. A cardiac monitor in a care home. A van full of groceries crossing rural postcodes. A public bin that messages the council when it’s full. These use cases span sectors...
Full Fibre Connectivity: What you need to know
People who sell insurance battle with an eternal challenge. At a glance, which is all most people give to the detail when they buy insurance, two competing policies can seem more or less the same....
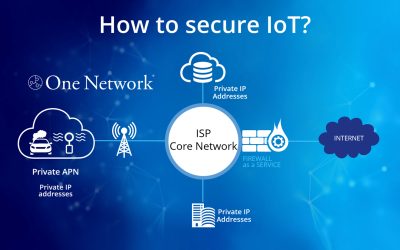
Beyond the SIM. Why IoT connectivity demands private network solutions
Whether it’s wearable health monitors, environmental sensors, or fleet management systems, IoT devices have become essential tools across public sector services IoT devices rely on a stable network...
Five IoT Security Myths Debunked
There are billions of connected IoT devices worldwide. These numbers show no sign of slowing down – with devices used across several industries and with transformative power, whether for security...
Security is A Boardroom Blind Spot That Must Be Fixed
Dear Business Leaders, Cybersecurity is one of the biggest existential threats to modern business, yet it remains a blind spot in too many boardrooms. Look around your next senior management...
A day in the life of a Spitfire Project Manager
Have you ever wondered what the person dealing with your installation does in a day? Matthew Ndudim joined us in 2023 as a Project Manager. He is thoroughly enjoying the variety of his role and...
In-Depth look at IoT: Market Trends and Security
The growth of the Internet of Things (IoT) is unquestionable, with many sources documenting the scale of this with some eye-catching statistics. For example, the Ericsson Mobility Report 2023 states...
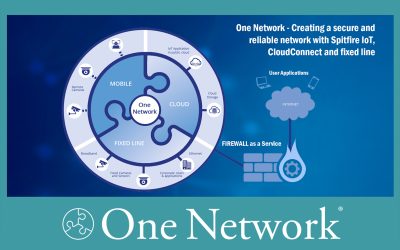
One Network – Redefining IoT Connectivity
Designed with IoT applications at its core, One Network is a bespoke network solution that integrates fixed line, 4G/5G mobile and on-net connections to cloud hosting platforms like Amazon Web...
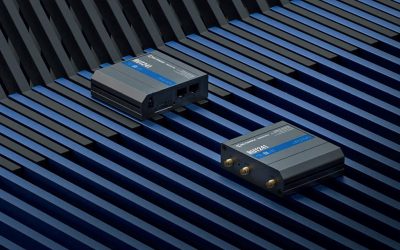
Mobile Data – Teltonika Router Solutions
As the demand for mobile data solutions continues to grow, Spitfire has partnered with Teltonika to ensure we can provide a router that meets any technical solution requirement at an appropriate...
Spitfire’s Full MVNO Launch – A New Era in Connectivity
On a sunny London afternoon on the 3rd October, atop the BT Tower, colleagues and Partners celebrated the official launch of Spitfire’s new implementation of their Full MVNO (Mobile Virtual Network...
What do our new starters think?
We recruit across the business for many exciting opportunities to join us at Spitfire Network Services. It’s a fantastic opportunity to join a fast-moving Telecoms and IP Engineering industry. Some...